A New Kind of Phishing Threat
Traditional phishing websites are typically static clones of well-known login pages — convincing enough to fool casual users, but relatively easy for security firms and anti-abuse activists to identify and take down. A newly documented phishing-as-a-service platform called Starkiller sidesteps both of those weaknesses entirely, and in doing so represents a meaningful escalation in how credential theft is carried out.
Rather than hosting a fake copy of a target's login page, Starkiller loads the real login page from the legitimate site and acts as a man-in-the-middle relay between the victim and the authentic service. Every username, password, multi-factor authentication (MFA) code, and session token the victim submits passes through attacker-controlled infrastructure — and is logged along the way.
How Starkiller Works
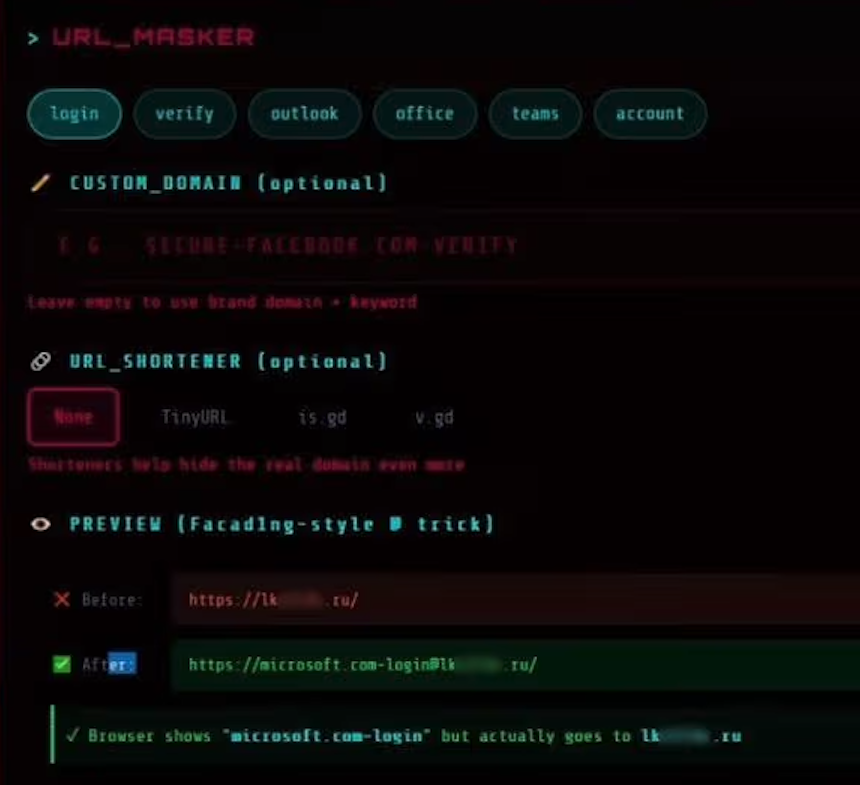
According to an analysis published by the security firm Abnormal AI, Starkiller allows its customers to select a brand they wish to impersonate — options include major platforms such as Apple, Facebook, Google, and Microsoft — and then automatically generates a deceptive URL designed to visually mimic the legitimate domain while routing all traffic through the attacker's infrastructure.
The URL trickery relies on an old but effective technique involving the "@" symbol. In a URL, everything before the "@" is interpreted as username data by the browser, while the actual destination is whatever follows the "@" sign. So a phishing link targeting Microsoft users might appear as login.microsoft.com@[malicious/shortened URL], making it look superficially legitimate at a glance. The service also supports integration with various URL-shortening services to further obscure the true destination.
Once a target clicks the link, Starkiller spins up a Docker container running a headless Chrome browser instance that loads the genuine login page from the target brand's actual servers. That container then functions as a reverse proxy, forwarding the victim's inputs to the real site and returning the real site's responses — creating a seamless, functional session that neither the victim nor the legitimate platform can easily distinguish from a normal login.
Real-Time Interception and MFA Bypass
Abnormal AI researchers Callie Baron and Piotr Wojtyla described the platform's capabilities in a blog post published on Thursday. "Every keystroke, form submission, and session token passes through attacker-controlled infrastructure and is logged along the way," they wrote.
Among the most alarming capabilities is Starkiller's ability to neutralize multi-factor authentication. Because the victim is genuinely authenticating with the real site — just through an attacker-controlled proxy — any MFA code they submit is forwarded to the legitimate service in real time. The resulting authenticated session cookies and tokens are then captured by the attacker.
"When attackers relay the entire authentication flow in real time, MFA protections can be effectively neutralized despite functioning exactly as designed." — Abnormal AI researchers Callie Baron and Piotr Wojtyla
This approach is particularly dangerous because it doesn't require the attacker to break or circumvent MFA in any technical sense. The authentication works correctly — it simply happens to flow through infrastructure the attacker controls.
An Enterprise-Grade Toolkit for Cybercriminals
Starkiller's feature set goes well beyond basic credential harvesting. The platform includes:
- Keylogger capture for every keystroke entered by the victim
- Cookie and session token theft enabling direct account takeover
- Geo-tracking of targeted individuals
- Automated Telegram alerts triggered when new credentials are captured
- Real-time session monitoring, allowing operators to live-stream a target's screen as they interact with the phishing page
- Campaign analytics including visit counts, conversion rates, and performance graphs — the same type of metrics dashboard a legitimate software-as-a-service (SaaS) platform would offer
An optional add-on feature will harvest email addresses and contact information from compromised sessions, with the collected data intended to fuel follow-on phishing campaigns against new targets.
The Jinkusu Threat Group
Starkiller is one of several cybercrime services operated by a threat group known as Jinkusu. The group maintains an active user forum where customers can exchange techniques, request new features, and troubleshoot their deployments — a structure that mirrors the customer support infrastructure of a legitimate software company.
This organizational model, sometimes described as "enterprise-style cybercrime tooling," is increasingly common among sophisticated threat actors. By productizing attack capabilities, groups like Jinkusu allow individuals with minimal technical skill to carry out attacks that would previously have required significant expertise.
Why This Matters for Defenders
Starkiller's architecture poses serious challenges for conventional phishing defenses. Because it loads real pages from legitimate domains rather than hosting static clones, it largely defeats two of the most widely used detection strategies: domain blocklisting and static page analysis. There are no fake pages to fingerprint and no lookalike domains to flag — at least not in the traditional sense.
The "@" trick in the URL is detectable with careful inspection, but many users — and even some automated systems — may not catch it, particularly when the link is further obfuscated through a URL shortener.
Abnormal AI's researchers concluded their report with a warning about the broader implications of platforms like Starkiller: "Starkiller represents a significant escalation in phishing infrastructure, reflecting a broader trend toward commoditized, enterprise-style cybercrime tooling. Combined with URL masking, session hijacking, and MFA bypass, it gives low-skill cybercriminals access to attack capabilities that were previously out of reach."
As with many successful cybercrime innovations, the operational simplicity and apparent effectiveness of Starkiller makes it likely that other threat actors will develop competing services modeled on its approach — further lowering the barrier to entry for would-be phishers and compounding the challenge for defenders.
Source: Krebs on Security